Professional Internet Solution 613167592 Guide
The 613167592 guide presents a disciplined framework for secure, efficient online operations. It links sections to concrete objectives and two-word focus phrases, preserving autonomy while ensuring relevance. Core tools promise immediate impact through modular, transparent metrics and repeatable steps, with clear emphasis on security and workflow optimization. Real-world workflows highlight incident response and change management, plus continuous improvement. Documentation supports rigorous validation and post-mortems, guiding responsible problem-solving while inviting further examination. The implications are substantive, yet the path forward remains contingent on disciplined execution.
Navigate the 613167592 Guide Effectively
To navigate the 613167592 Guide effectively, readers should start by mapping the guide’s structure and locating the key sections relevant to their objectives.
The approach emphasizes selective reading, noting discussion ideas and subtopic unrelated elements for context.
This method supports disciplined focus, two word phrases, and objective assessment, enabling autonomy while maintaining precise, analytical evaluation of relevant content.
Core Tools for Instant Impact
The guide moves from mapping and targeted reading into practical execution, presenting a concise set of tools designed to deliver immediate results.
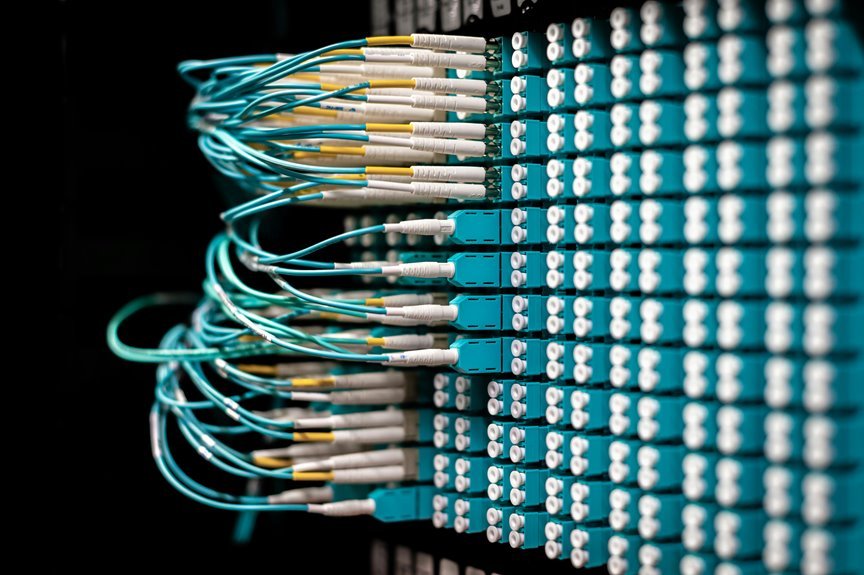
Core tools enable rapid deployment with minimal friction, emphasizing security protocols and workflow optimization.
They favor modularity, transparent metrics, and repeatable steps, allowing teams to act decisively while maintaining accountability, adaptability, and measurable progress toward clear, freedom-enhancing outcomes.
Practical Security and Efficiency Best Practices
Practical security and efficiency best practices focus on actionable measures that safeguard systems while streamlining operations. A detached evaluation highlights layered controls, minimal exposure, and responsible data handling. Privacy auditing reinforces accountability without hindering agility, while ongoing password hygiene reduces breach risk. Automated monitoring, clear access policies, and regular vulnerability reviews foster trust, independence, and resilient performance within evolving digital environments.
Real-World Workflows, Checklists, and Troubleshooting
Real-World Workflows, Checklists, and Troubleshooting outlines practical procedures that teams regularly follow to deliver consistent results. The analysis emphasizes disciplined data privacy, explicit incident response, and a clear integration strategy. It also highlights structured change management, standardized playbooks, and continuous improvement. Rigorous validation, documentation, and post-mortems enable predictable outcomes while preserving autonomy and a culture of responsible, freedom-oriented problem solving.
Conclusion
In the courtyard of progress, the 613167592 Guide stands as the quiet lighthouse, its beams tracing disciplined paths through foggy complexity. Tools gleam like compass needles, pointing to immediate impact and transparent metrics. Security stands as a steadfast lock, safeguarding every doorway. Real-world workflows unfold like measured steps on a map, each checklists’ tick a heartbeat of steady improvement. Symbolically, the guide turns chaos into architecture, privacy into practice, and autonomy into sustainable momentum.





